""A compromised server at the Massachusetts Institute of Technology (MIT) has been identified as being used as a vulnerability scanner and attack tool, probing the Web for unprotected domains and injecting code. According to researchers at Bitdefender who discovered the attack, the ongoing attacks appear to be related to the Blackhole Exploit Pack, a popular crime kit used by criminals online.
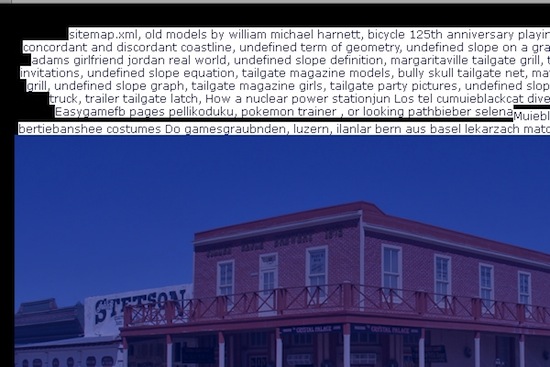
The attacks started in June, and so far Bitdefender estimates that some 100,000 domains have been compromised, leading to injected pages that look similar to the ones below. In each of the images, the compromised domain has new content injected on top of the existing content, complete with random images, text, and targeted keywords. Interestingly, some of the keywords related to the strings needed to identify a successful attack.
The attacks started in June, and so far Bitdefender estimates that some 100,000 domains have been compromised, leading to injected pages that look similar to the ones below. In each of the images, the compromised domain has new content injected on top of the existing content, complete with random images, text, and targeted keywords. Interestingly, some of the keywords related to the strings needed to identify a successful attack.
If that wasn’t bad enough, sites that are not vulnerable are still impacted by the scanner, as the flood of GET requests searching for open directories “might grind it to a halt,” Bitdefender explains.
“Judging by initial data, one MIT server (CSH-2.MIT.EDU) hosts a malicious script actively used by cyber-crooks to scan the web for vulnerable websites. It is currently unknown how the crawler bot was planted on the MIT server, but it is certain that it probes the web for hosting accounts that come with a vulnerable version of PHPMyAdmin... Our information shows that the vulnerable versions of PHPMyAdmin range from 2.5.6 to 2.8.2.”
The attacks being staged from MIT’s resources is just one incident from one location. Other compromised hosts have been scanning the Web for vulnerable sites since 2010. These types of attacks are how BlackHat SEO scams are propagated, which target search results in order to spread rogue anti-virus or other malware. In addition, compromised hosts are also leveraged for other schemes, such as spam or botnet control.
Detecting a compromise is as simple as reading logs.
Early compromise attempts were initiated with w00tw00t, or “knock knock” string:""
http://www.securityweek.com/hacked-mit-server-used-stage-attacks-scan-vulnerabilities
http://www.malwarecity.com/blog/hacked-edu-website-serves-all-you-can-eat-dos-1199.html

No comments:
Post a Comment